Amazon SCS-C02 Exam Dumps
Vendor: Amazon
Exam Code: SCS-C02
Exam Name: AWS Certified Security - Specialty (SCS-C02)
Certification: Amazon Certifications
Total Questions: 830 Q&A
( View
Details)
Updated on: Aug 14, 2025
Note: Product instant download. Please sign in and click My account to download your product.
- 99.5% pass rate
- 12 Years experience
- 7000+ IT Exam Q&As
- 70000+ satisfied customers
- 365 days Free Update
- 3 days of preparation before your test
- 100% Safe shopping experience
- 24/7 Support
Amazon SCS-C02 Last Month Results
Free SCS-C02 Exam Questions in PDF Format
- File
- Size
- Amazon_leads4pass_SCS-C02_by_Ahmed_Nasser_665.pdf
- 214.59 KB
- Amazon_leads4pass_SCS-C02_by_Kandre_621.pdf
- 214.91 KB
- Amazon_leads4pass_SCS-C02_by_syaiful_665.pdf
- 228.07 KB
- Amazon_leads4pass_SCS-C02_by_mohan_665.pdf
- 253.62 KB
- Amazon_leads4pass_SCS-C02_by_kristin_697.pdf
- 288.29 KB
- Amazon_leads4pass_SCS-C02_by_mbmk4u_610.pdf
- 250.71 KB
SCS-C02 Online Practice Questions and Answers
For compliance reasons, an organization limits the use of resources to three specific IAM regions. It wants to be alerted when any resources are launched in unapproved regions.
Which of the following approaches will provide alerts on any resources launched in an unapproved region?
A. Develop an alerting mechanism based on processing IAM CloudTrail logs.
B. Monitor Amazon S3 Event Notifications for objects stored in buckets in unapproved regions.
C. Analyze Amazon CloudWatch Logs for activities in unapproved regions.
D. Use IAM Trusted Advisor to alert on all resources being created.
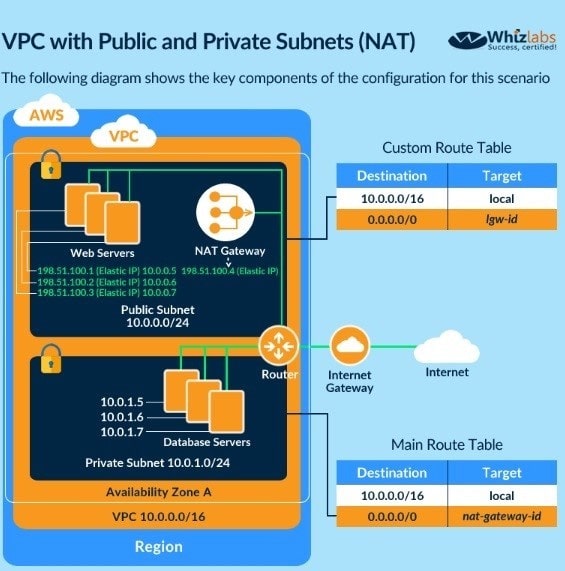
You are planning on hosting a web application on IAM. You create an EC2 Instance in a public subnet. This instance needs to connect to an EC2 Instance that will host an Oracle database. Which of the following steps should be followed to ensure a secure setup is in place? Select 2 answers.
A. Place the EC2 Instance with the Oracle database in the same public subnet as the Web server for faster communication
B. Place the EC2 Instance with the Oracle database in a separate private subnet
C. Create a database security group and ensure the web security group to allowed incoming access
D. Ensure the database security group allows incoming traffic from 0.0.0.0/0
You need to create a Linux EC2 instance in IAM. Which of the following steps is used to ensure secure authentication the EC2 instance from a windows machine? Choose 2 answers from the options given below.
A. Ensure to create a strong password for logging into the EC2 Instance
B. Create a key pair using putty
C. Use the private key to log into the instance
D. Ensure the password is passed securely using SSL
Why SCS-C02 Dumps Are Worth It
Hannah Johnson
Leads4Pass is one of the best websites I have ever used. It only took me 3 days of preparation to complete my goal plan. Not only that, I was successful with high scores.
Joel C
It was the 16th when I purchased the Leads4Pass materials. They updated the materials on the 18th. When I asked them to send me the latest materials, they quickly sent me the latest ones. The new materials included several of the latest core question types. Finally, I succeeded. Six of the new core questions were completely matched. Thank you!
Martha W
I have used free materials, the privacy is poor, the public content matching rate is too low,I gave up on them because they failed me once. Leads4Pass was recommended by a friend. Both the privacy protection and the preciousness of the materials are very high. By the way, I won this time.
David Frazier
There is nothing more satisfying than success! Their question types are very similar, and they were very helpful to my progress in answering questions during the exam. Thank you.
Dolores N
I need to take multiple certification exams for my organization. There are so many certification exams that I can't help but choose supporting materials. I have tried multiple platforms with some success and failure. In the end, I chose Leads4Pass. It was instant for me. Effective materials are where the real value lies.
Helen Kovac
I was despised by a close friend until he failed twice and I passed once and then he changed his mind. He shared his failure experience with me. He told me that he had been learning through books and looking for free materials. These outdated contents could not really help him. Later I recommended him Leads4Passs and he also succeeded.
Raymond I
I was lucky enough to choose Leads4Pass for the first time. I used their VCE tool to learn, and it was really easy and efficient. I think what’s really amazing is that they can ensure that all materials are industry-leading, which is really amazing.
Leads4Pass Amazon Certifications SCS-C02 Exam Analysis
The following table comprehensively analyzes the quality and value of Amazon Certifications SCS-C02 exam materials.

100% safe shopping
100% real and effective
100% money back guarantee
Leads4Pass guarantee comes from more than 10 years of experience and reputation

 Printable PDF
Printable PDF